Take Control of Cyber Risks with Continuous Threat Exposure Management (CTEM)
Continuously uncover vulnerabilities, validate defenses, and reduce risks to safeguard critical assets.
What is Continuous Threat Exposure Management (CTEM)?
CTEM is a security framework for identifying, assessing, and managing threats across an organization’s attack surface. However, a framework alone isn’t enough. Adversarial Exposure Validation (AEV) makes CTEM actionable by continuously testing and validating security controls against real-world attack scenarios. With AEV, you can move beyond theoretical risk management to actionable security improvements, reducing exposure and strengthening defenses before threats can be exploited.
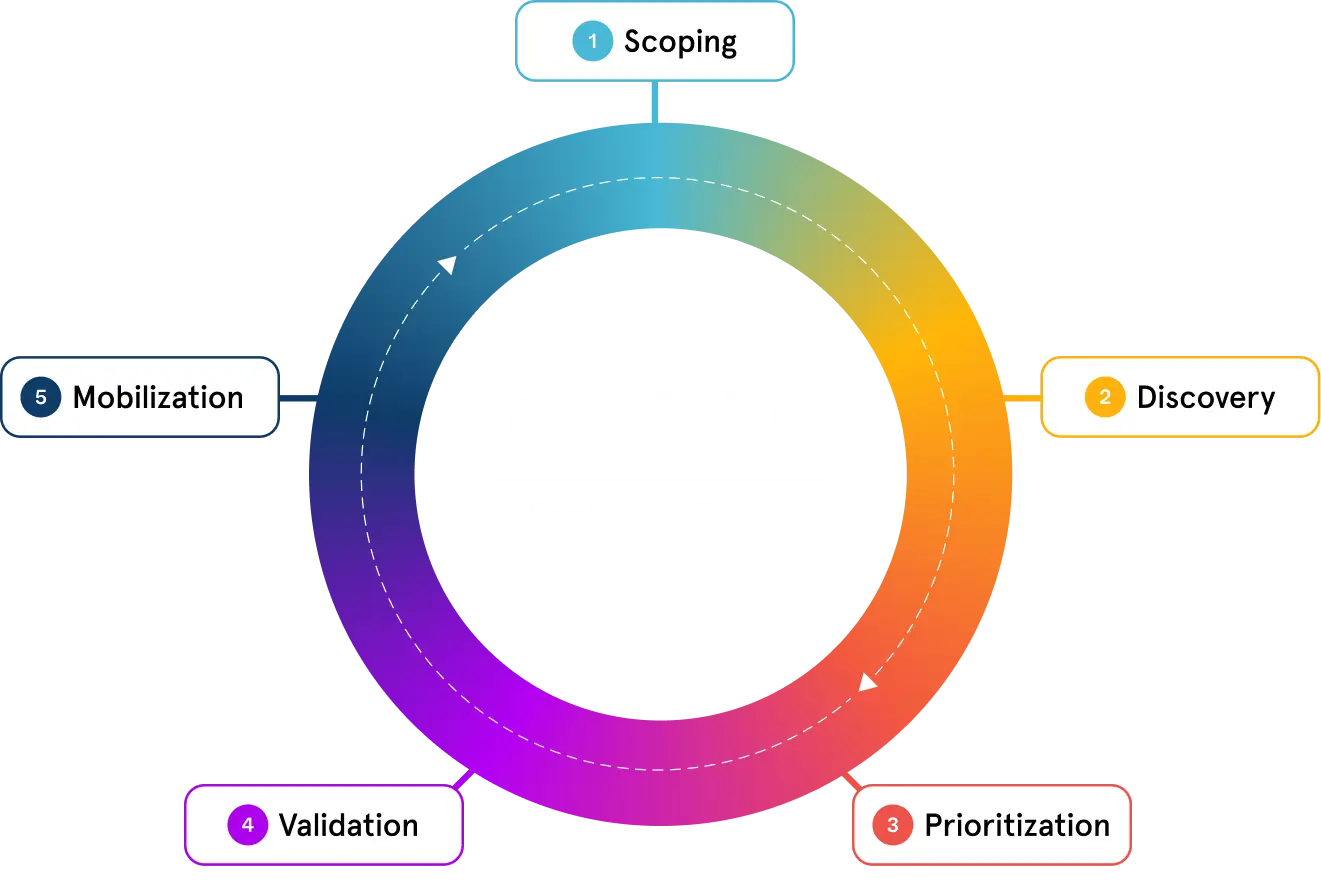
CTEM Framework
The five stages of CTEM provide a clear roadmap for identifying, prioritizing, and validating exposures, ensuring security teams focus on the most critical threats while strengthening defenses against real-world adversary tactics.
“By 2026, organizations that prioritize their security investments based on a continuous exposure management program will be 3x less likely to suffer a breach.”
How AttackIQ Powers CTEM
AttackIQ’s Adversarial Exposure Validation Platform operationalizes CTEM by delivering advanced automation, actionable insights, and real-world adversary emulations—all seamlessly integrated to scale your security operations.
White Paper
From Security Gaps to Continuous Validation
Point-in-time security tests aren’t enough. Continuous validation ensures your defenses are always ready by proactively identifying and addressing threat exposure. Learn how AEV enhances your security posture through the five stages of CTEM—before attackers can exploit them.
CTEM in Action
Proactive Threat ManagementGain real-time visibility into vulnerabilities and attack paths, prioritizing threats that matter most.
- Automate threat discovery and risk assessment.
- Validate defensive measures with adversarial emulations.
- Focus resources on high-impact risks to minimize exposure.
Security Tool OptimizationEnhance the performance of your existing tools to improve detection and prevention capabilities.
- Identify gaps and configuration drift across security controls.
- Validate tool effectiveness with real-world scenarios.
- Ensure alignment with the MITRE ATT&CK Framework.
Compliance Validation and ResilienceStreamline compliance processes while building long-term resilience.
- Continuously validate readiness for regulatory standards like NIST and DORA.
- Automate reporting to meet audit requirements.
- Demonstrate measurable improvements to stakeholders.
Your Security, Your Way
Choose the adversarial exposure validation solution that fits your needs and scale your security operations with flexibility, control, and comprehensive protection.
Ready to Experience Continuous, Automated Security Testing?
Take the guesswork out of threat exposure management. Validate your defenses with real-world attack scenarios and focus on what matters most—managing your risk.
