Cut the Noise. Validate Continuously. Strengthen Resilience with Adversarial Exposure Validation
Reduce Your Risk Exposure

Trust Nothing, Validate Everything
Continuously test and validate security controls against real adversary tactics to ensure defenses are both resilient and effective. Leverage actionable insights from real-time threat intelligence to prioritize critical exposures.
Impact to Customers
Gain unparalleled visibility, efficiency, and control for unmatched protection, cost savings, and peace of mind.
AttackIQ Adversarial Exposure Validation Platform
Strengthen your defenses with the industry’s most comprehensive security validation platform.
Breach and Attack Simulation
Powering Security Control Validation
Test and validate your security controls against real-world threats to ensure your defenses are resilient and effective against advanced adversary techniques.
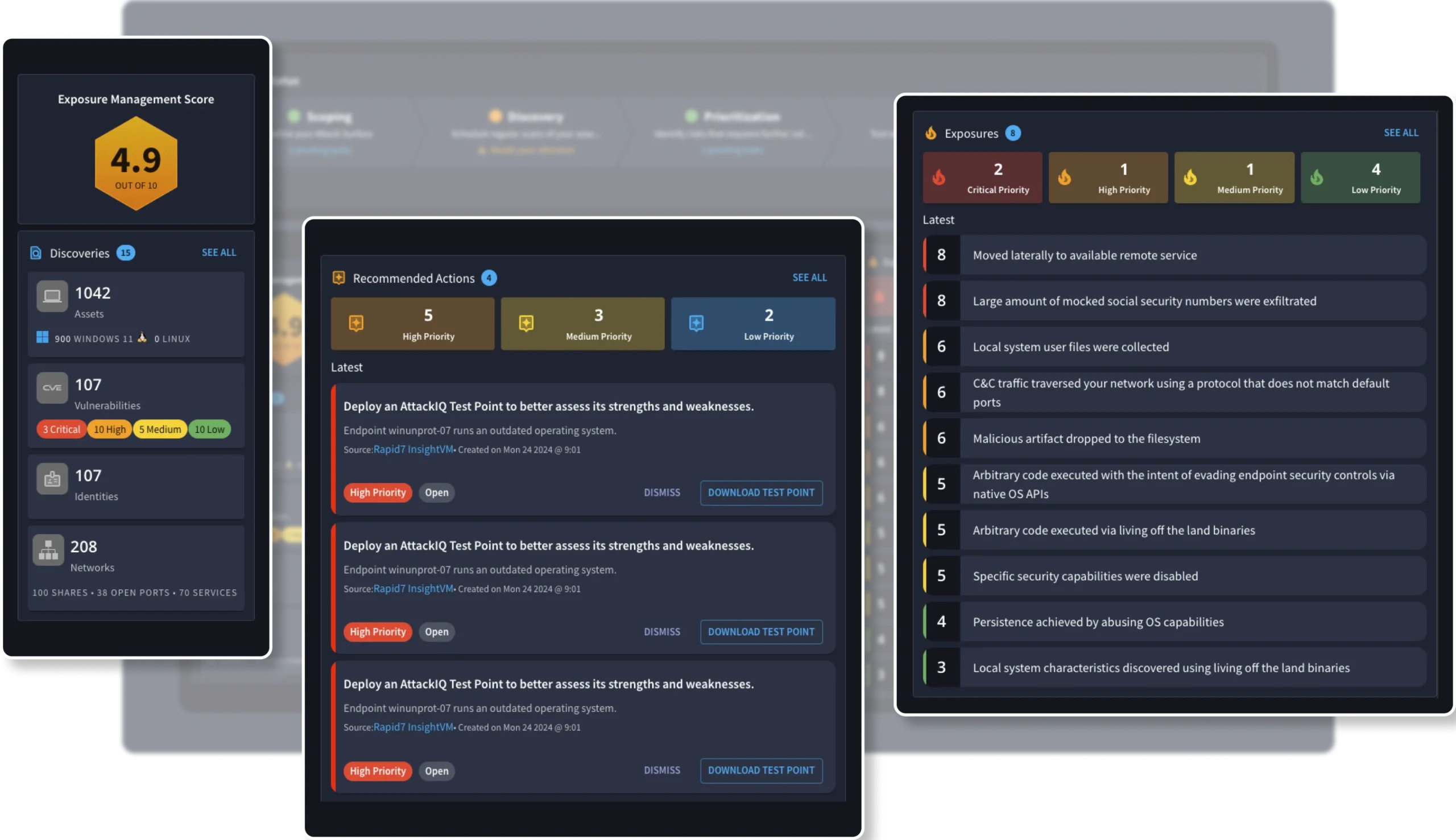
Continuous Threat Exposure Management
Access actionable insights to enhance your CTEM strategy and improve security resilience.
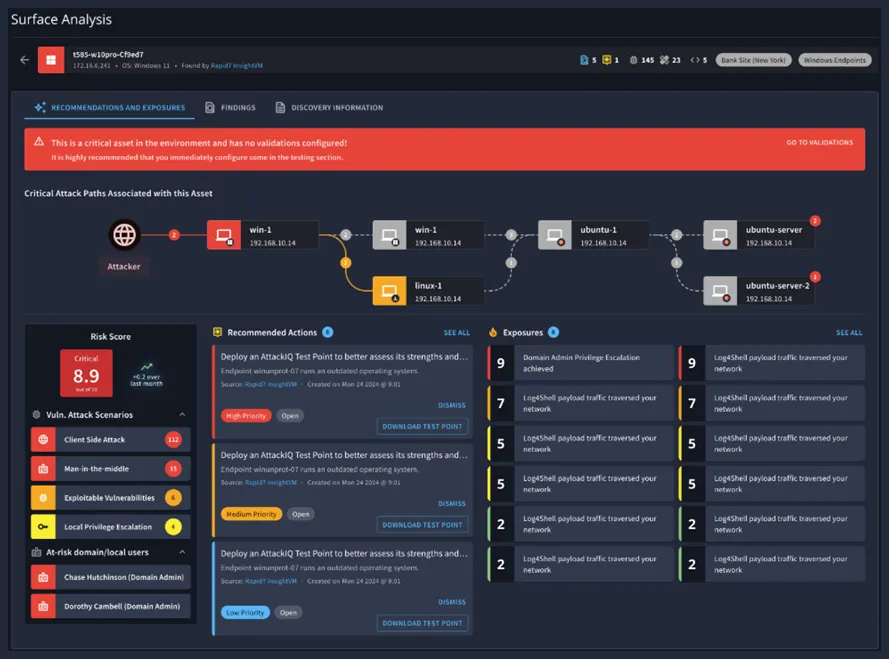
Attack Surface Management
Continuously discover your attack surface to tailor validation tests to your environment.
Attack Path Management
Visualize exploitable attack paths and address gaps before they can be exploited.
Active Threat Monitoring
Continuously assess your environment for emerging threats threatening your environment.
CTEM Analytics
Access actionable insights to enhance your CTEM strategy and improve security resilience.
CISO Dashboard
Provide executives with a score-based view that highlights risks, progress, and improvement areas.
AttacklQ Virtual Advisor (AVA)
Leverage AI to navigate testing, analyze results, and get actionable steps to improve your posture.
Your Security, Your Way
Choose the adversarial exposure validation solution that fits your needs and scale your security operations with flexibility, control, and comprehensive protection.
The AttackIQ Advantage
AttackIQ is at the forefront of Adversarial Exposure Validation, helping organizations to validate security controls in real time and understand the true risk of vulnerabilities for a proactive, threat-informed security posture.
Building Security into Every Layer
AttackIQ’s AEV platform is designed with proactive security at its core. We integrate industry-leading practices to ensure you are protected from evolving threats at every layer of your security operations.
 Secure by Design PledgeSecurity is embedded into every layer of our platform, providing comprehensive protection from the start.
Secure by Design PledgeSecurity is embedded into every layer of our platform, providing comprehensive protection from the start. Threat-Informed DefensePartnering with MITRE Center for Threat-Informed Defense to develop and field-test adversary emulation concepts, strengthening decision-making and risk management with real-world insights.
Threat-Informed DefensePartnering with MITRE Center for Threat-Informed Defense to develop and field-test adversary emulation concepts, strengthening decision-making and risk management with real-world insights.Never Settle for Uncertainty – Validate Your Defenses
Take the guesswork out of threat exposure management. Validate your defenses with real-world attack scenarios and focus on what matters most—managing your risk.
