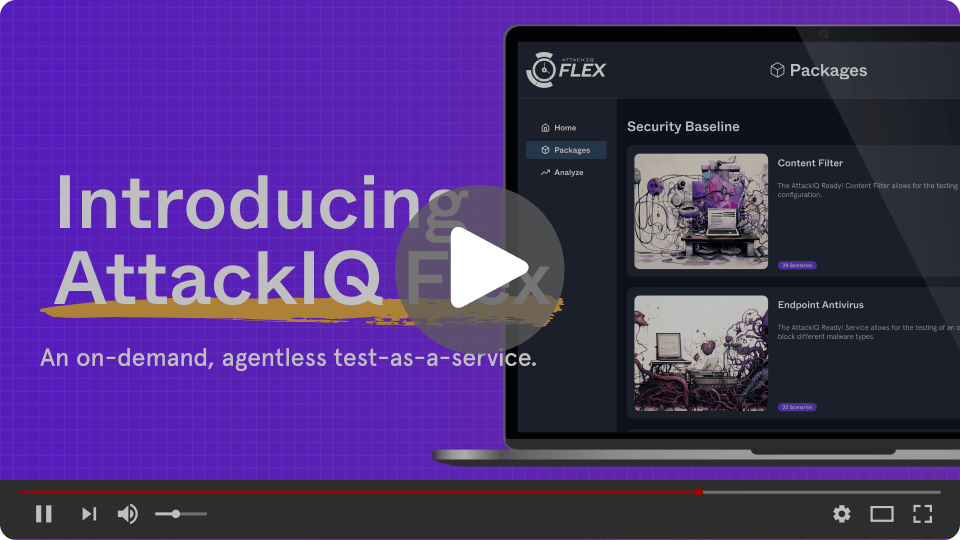
Secure, Scalable, and Simple Adversary Emulation
Run production-safe adversary emulation to validate the effectiveness of your security controls.

Cost-Effective and Scalable
Flexible, pay-as-you-go pricing that scales to your testing needs.

Instant Security Validations
Get actionable insights in minutes, helping you quickly identify and resolve security gaps.

Complete Visibility
Self-contained test packages you can run anywhere on any device.
Simplified Testing Experience
Pentest-grade assessments you can run at the click of a button with an intuitive user experience.
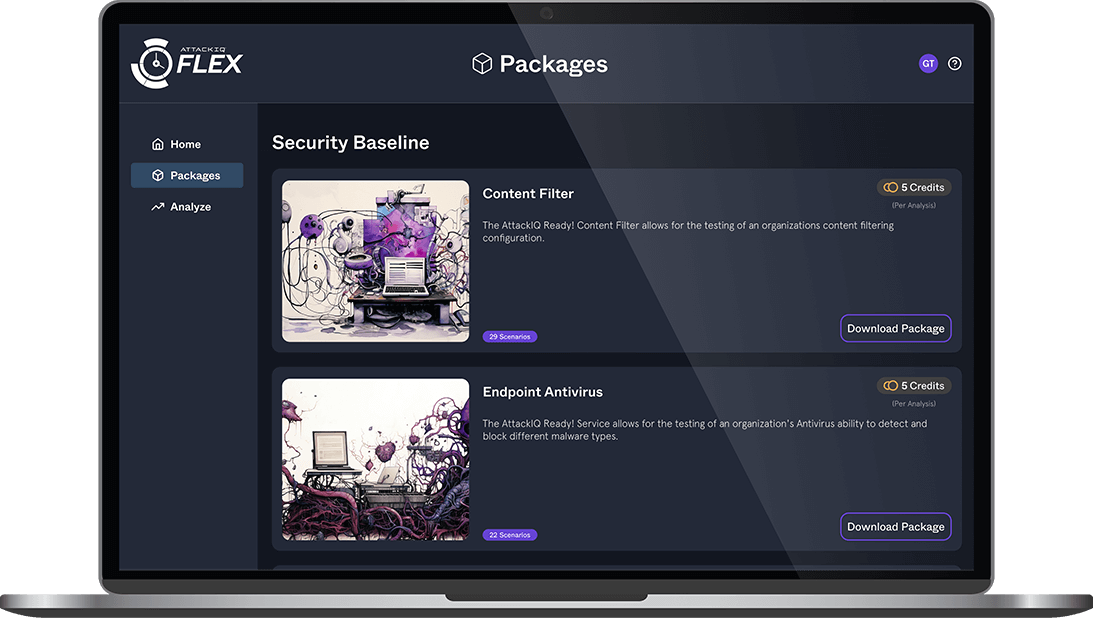
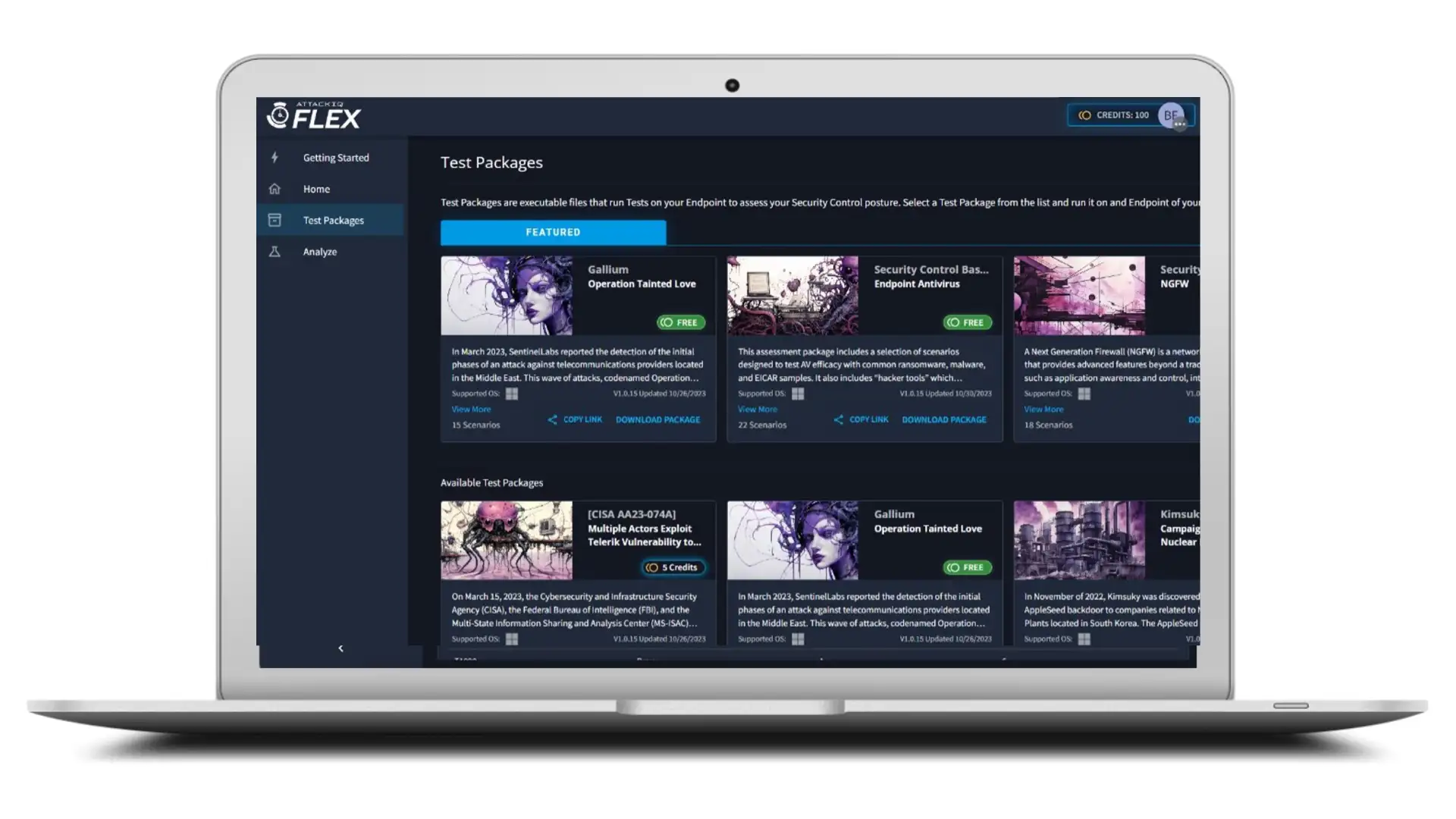
Security Control Testing Made Easy
Lightweight and agentless, AttackIQ Flex lets you start testing in three simple steps—no setup or training required.
- Choose Your Tests: Select from full adversarial testing and security control baselines to validate your defenses
- Analyze Your Results: See overall performance with metrics broken down by tactic, technique, and procedure using adversarial exposure validation to identify weaknesses
- Reduce Adversary Exposure: Implement fixes using the provided mitigation recommendations and detection rules to prevent the attack with threat emulation
Real-World Adversary Emulations
- Realistic Adversary Emulations: Test your defenses against real world adversary TTPs with emulations designed by industry leading researchers.
- Security Control Testing: Out of the box security control tests designed to assess the most critical functions of your NGFW, EDR, network security, and more.
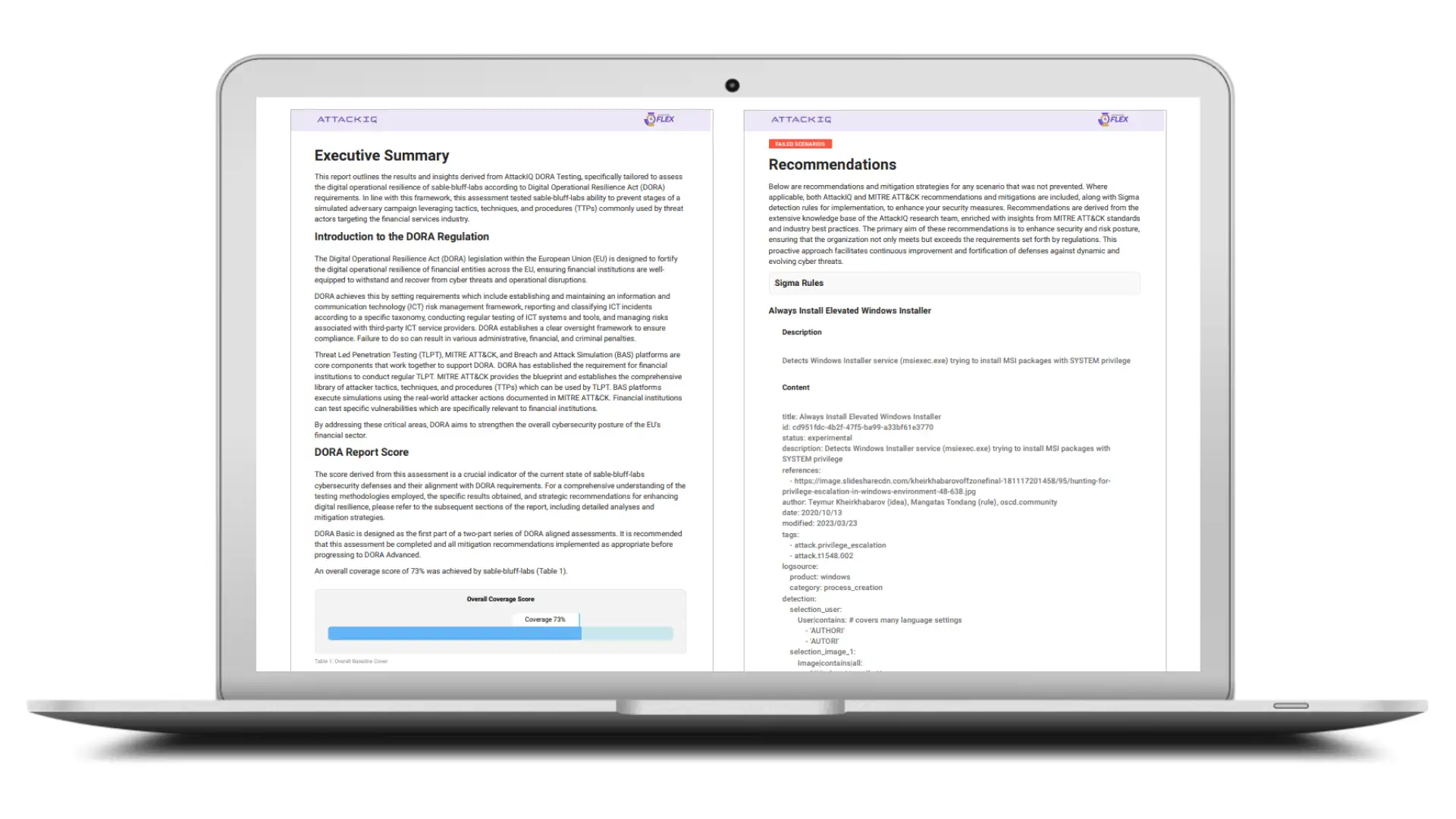
- Compliance-Aligned Testing: Run tests aligned with key frameworks like NIST and DORA to ensure compliance and meet industry standards.

Real-Time Visibility and Insights
- Intuitive Results: Clear insights into your overall security performance, weaknesses, and performance over time.
- Actionable Reports: Comprehensive reports with detailed results by attack stage, TTP, and executive insights.
- MITRE ATT&CK-Mapped Reporting: Close alignment with MITRE ATT&CK ensures that security teams can easily understand and communicate results in a common language.
Real-Impact Mitigation Guidance
- Tailored Recommendations: Receive precise, step-by-step guidance on how to remediate each identified gap including recommendations from adversary emulation tools, ensuring a swift and effective response
- Prioritized Action Steps: Focus on your most critical gaps first, helping your team allocate resources where they’re needed most.
- On-Demand Expert Support: Access AttackIQ’s industry-leading experts for additional testing support and personalized guidance, ensuring best practices and optimized results.
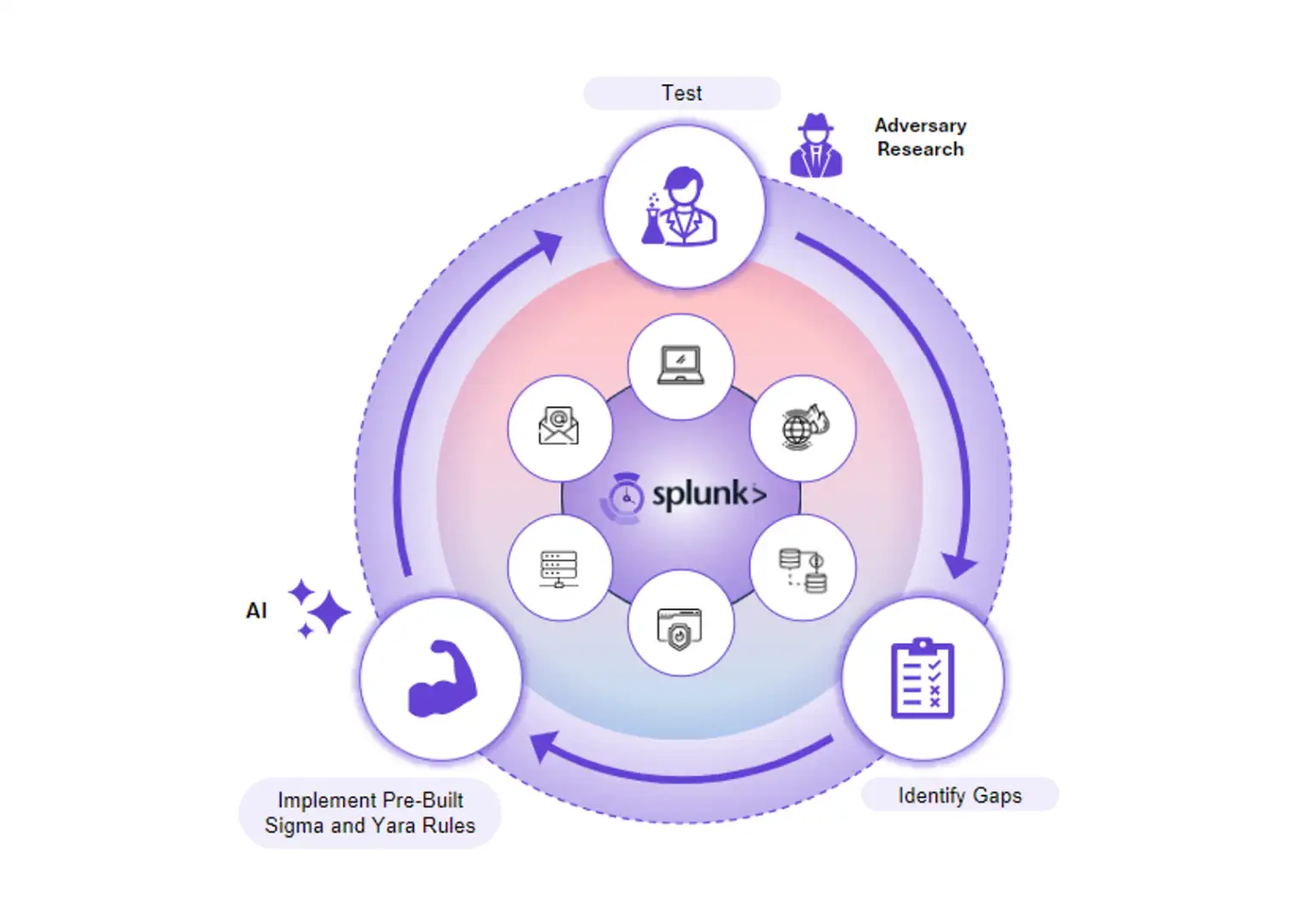
Seamless Integration with Splunk
- Detection Visibility: Ensure that your security controls can reliably identify an attack, even when prevention fails.
- Fix Detection Gaps Faster: Out-of-the-box Yara and Sigma rules that can be immediately deployed to your security controls.
- Validate Detection Pipeline: Ensure that your SIEM is accurately capturing and analyzing activity from your security controls.
“Once you use it, you’ll never want to use anything else again.”
Richard Wadsworth, Cybersecurity Professional
AttackIQ Flex Pricing
AttackIQ Flex provides an economical means of validating security controls without the need for expensive and time-consuming manual testing. With a pay as you go consumption model, you can test as little or as much as you want and across elements of your business.
Free
Best for people just getting started with Breach & Attack Simulation.
- Access to Free Testing Packages
- Access to Adversary Research
$300
Best for people looking to test on an intermittent basis.
- Credit-based Purchases
- Access to Volume-based Discounts
- Access to Adversary Research
$4,995/mo
Best for people looking to do comprehensive ad-hoc testing.
- Access to Unlimited Testing (30 Days)
- Access to Adversary Research
- 1 Hour of Professional Services
Get in Touch
Best for people looking to do programmatic testing all year.
- Access to Unlimited Testing
- Access to Adversary Research
- 6 Hours of Professional Services
Contact Us
AttackIQ Flex Yearly Plan
Comprehensive Testing Modalities for Real-World Defense
AttackIQ Flex provides a robust suite of testing options, enabling your team to validate and strengthen defenses against real-world threats.
“With a couple clicks I was able to setup an account, download the agent and run a test inside our environment… And, I just love the ad hoc, pay as you go nature of the product which fits more in line with our budget and scale.”
Common Questions
There are innumberable uses cases for Flex. Below are some initial examples.
- Zero trust. Perform regular testing to validate the security of critical assets.
- SMB. Organizations with small network and security stacks, limited in house resources want to include security testing as part of security program
- Red team augmentation. Automate the scripting and execution of attack scenarios and penetration tests, allowing red teams to comprehensively test security controls, identify vulnerabilities, and provide mitigations
- Purple teaming augmentation. Design and execute attack scenarios against defenders with immediate feedback into people, process, and technology efficacy
- Regular self-managed security validation. Basic security validation and breach and attack simulation
- Fully managed security validation program. Conduct regular security validation but doesn’t have the staff to support in house testing
- Security posture assessment. Use Flex to validate security controls by scaling as many test points as you need for a representative sample of your environment.
- Managed service provider. Insurance provider or underwriter wants insuree to run a risk assessment on their network to determine coverage.
- Network consolidation, including M&A activity. Acquirer or parent organization wants to quickly bring on new branch networks into the corporate umbrella. Deploying agents takes too long for the request.