Iranian Cyber Threat Escalation: Preparing for Asymmetric Response through Adversarial Validation Emulation
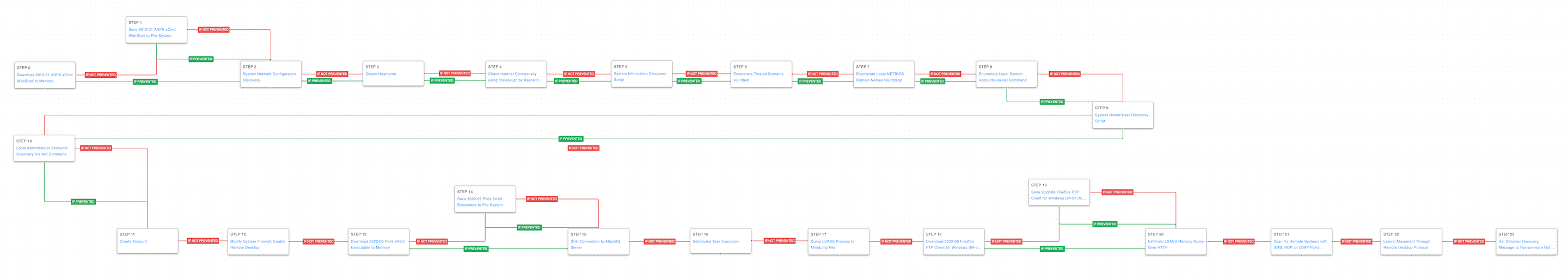
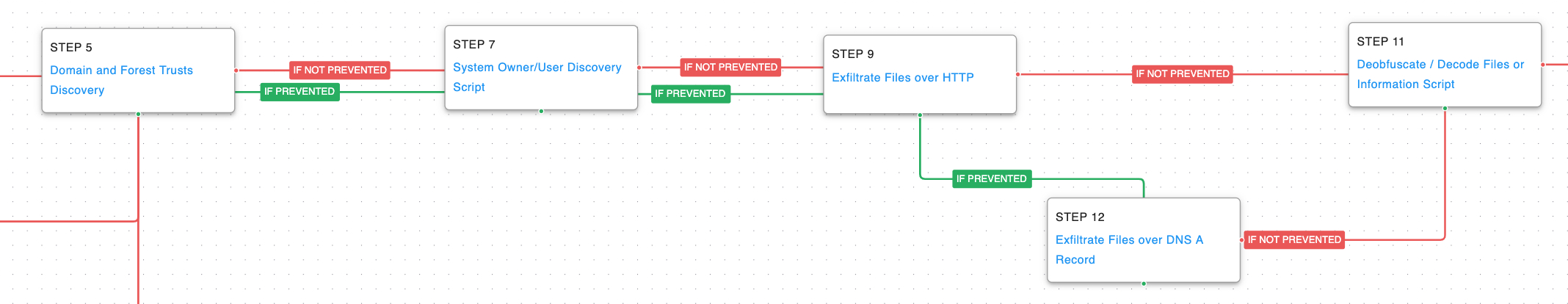
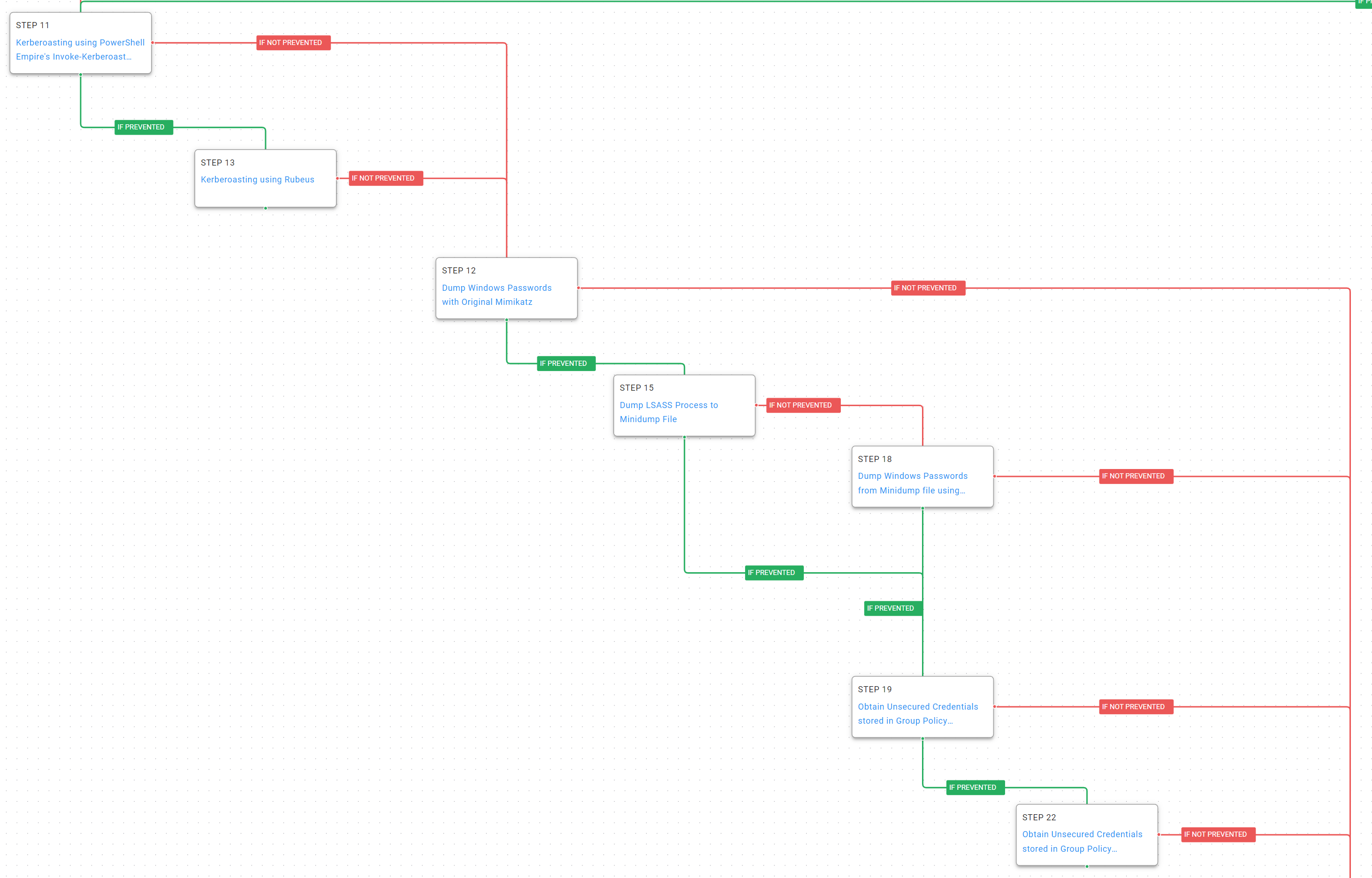
Amid rising tensions after Israeli and U.S. strikes on Iranian nuclear sites, experts warn of increased Iranian cyber retaliation. With limited conventional options, Iran is expected to rely on cyberattacks against U.S. infrastructure and defense sectors. DHS has issued alerts on threats from state-backed hackers and proxies. AttackIQ continues to help organizations test and strengthen their defenses.